Avast For Mac Disable Https
Click the menu bar icon and chose open Avast from the list of the context menu. Bigquery client python. Now click on security option in the menu bar and then select uninstall Avast option. Click on the uninstall option and continue.
Dolby® CineAsset Player is a software-based media player used to review digital cinema packages (DCPs) without the need for a digital cinema server. In addition to playing back any DCP, Dolby CineAsset Player can also play back many popular multimedia file types. The Pro version of Dolby CineAsset Player allows for the playback of encrypted, 3D, and 4K DCPs, as well as subtitle rendering. Find out more information about Dolby Audio macOS support on Dolby Developer. Login Required. You must have a Dolby Developer account to acces that content. Log in below to continue. Don’t have an account? Creating an account is free and easy! Dolby Atmos Dolby Vision HDR; Mac Pro (2019). Other manufacturers that support Atmos are Lenovo, Razer, and Acer. Apple devices, such as the new iPad Pro and iPhones, as well as Macs, support it. Other major manufacturers that support Dolby Atmos are Lenovo, HTC, LG, and ZTE. For the full list of manufacturers that support Dolby Atmos for smartphones and laptops, click here or here. Plex Player for 4K with Atmos. Plex Player for 4K with Atmos. I'm sure this question has been posted before, but I figure things always change so worthwhile asking now. I'm looking for Plex media players that will support 4k video output with full Dolby Atmos (7.1.4) passthrough, that is reliable with an easy to use interface. Macbook pro hdr. Dolby® CineAsset Player is a software-based media player used to review digital cinema packages (DCPs) without the need for a digital cinema server. In addition to playing back any DCP, Dolby CineAsset Player can also play back all file types supported by Dolby CineAsset, including many popular multimedia types.
hi, firefox has always used it's 'own' certificate store on all platforms, so this is to be expected. since root certificates are an extremely sensitive area (which would allow an attacker to 'take over' the secure web for affected trust stores), a little bit of 'competition' and independent implementations are beneficial to the health of the web in my view.avast would have to insert its certificate into the firefox trusted root ca store for this to work without any issues like the error message you are seeing.
By Malcolm Owen
Monday, January 27, 2020, 07:46 am PT (10:46 am ET)
Avast offers a selection of free and paid-for antivirus and security tools, in both free and in paid-for formats. The tools are popular, with more than 435 million active users per month using it on Macs, PCs, and mobile devices, to keep their data safe from harm.
As part of its offerings, Avast's software provides the option to opt-in to allowing the firm to collect some types of user data, which it then sells on via subsidiary Jumpshot. An investigation by Vice and PC Mag using leaked user data, contracts, and other documents has revealed both the extent of these sales, as well as the breadth of the data being sold by the firm.
Data acquired for the investigation revealed the information collected by Avast is wide-ranging, including Google searches, location look-ups and GPS coordinates from Google Maps, LinkedIn pages, and YouTube video listings. More disturbingly, records porn site visits that are anonymized offer the date and time the user visited the sites, as well as search terms and viewed videos in some instances.
Despite the efforts to anonymize the data, some experts claimed the highly specific browsing data could be used to find out identities.
A wide net
The amount of data being collected may not be well advised to consumers of Avast, with the investigation advised by multiple users they were not aware of the sale of said browsing data.
The subsidiary claims it has data from 100 million devices, with the investigation claiming Jumpshot repackages data collected from Avast into a number of different packages. This also includes a so-called 'All Clicks Feed' option, where clients paid millions of dollars to be able to track a user's behavior and movement across websites.
The list of clients include many major firms, such as Google, Yelp, Microsoft, and Pepsi.
Collecting the data was, until recently, conducted via Avast's browser plugin, one that provides warnings to the user about suspicious and malicious websites. A report by security researcher and AdBlock Plus creator Wladimir Palant in October revealed the plugin was used to harvest data in October, prompting Mozilla, Opera, and Google to remove access to Avast's extensions.
Avast told the investigation in a statement it has stopped providing browsing data collected by the extensions to Jumpshot.
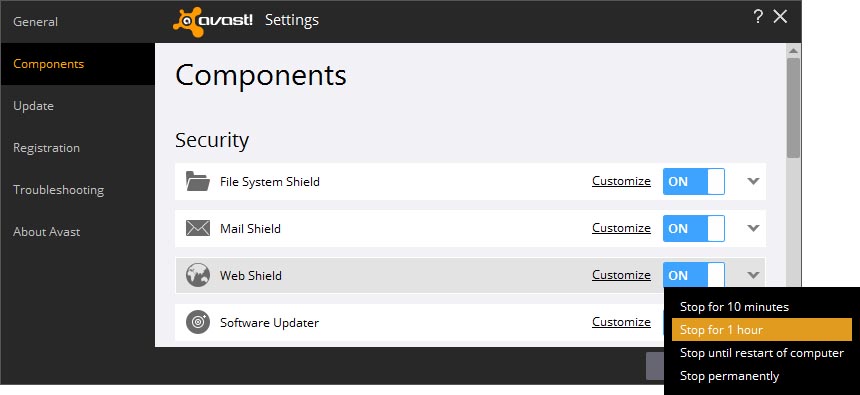
The investigation further found from a source and leaked documents that Avast is still performing harvesting, but via the anti-virus software itself, rather than the browser plugins. In the last week, an internal document reveals Avast has started asking users of the free antivirus tool to opt-in to data collection once again.
'If they opt-in, that device becomes part of the Jumpshot Panel and all browser-based internet activity will be reported to Jumpshot,' a line of text from an internal handbook advised. The data collected, according to the document, would answer questions about what URLs a user visited, as well as when and in what order.
Lucrative data
The data is a lucrative income for Avast. In copies of contracts with Jumpshot clients, one marketing firm paid over $2 million for data access in 2019, which provided an 'Insight Feed' for 20 domains from 14 countries around the world.
That data included the inferred gender of users based on browsing behavior, their age, the 'entire URL string' with personally identifiable information removed, and other details. Device IDs are 'hashed' to prevent identification of individuals by clients, but as the device IDs do not change for a user unless they completely reinstalled Avast tools, this could allow for a large swathe of data on one user to be built up over time, leading to possible identification down the line.
Avast informed the investigation 'because of our approach, we ensure that Jumpshot does not acquire personal identification information, including name, email address, or contact details, from people using our popular free antivirus software.' The company went on in a statement to reiterate users had the ability to opt out of sharing data, and that it had started 'implementing an explicit opt-in choice for all new downloads of our AV' as of July 2019, with all existing free users prompted to make a choice by February 2020.
It was also insisted Avast complies with the California Consumer Privacy Act and Europe's GDPR across its entire global user base. 'We have a long track record of protecting users' devices and data against malware, and we understand and take seriously the responsibility to balance user privacy with the necessary use of data,' the statement pressed.